Future of Microsoft Entra External ID
Part 3: Roadmap, Best Practices, and Recommendations
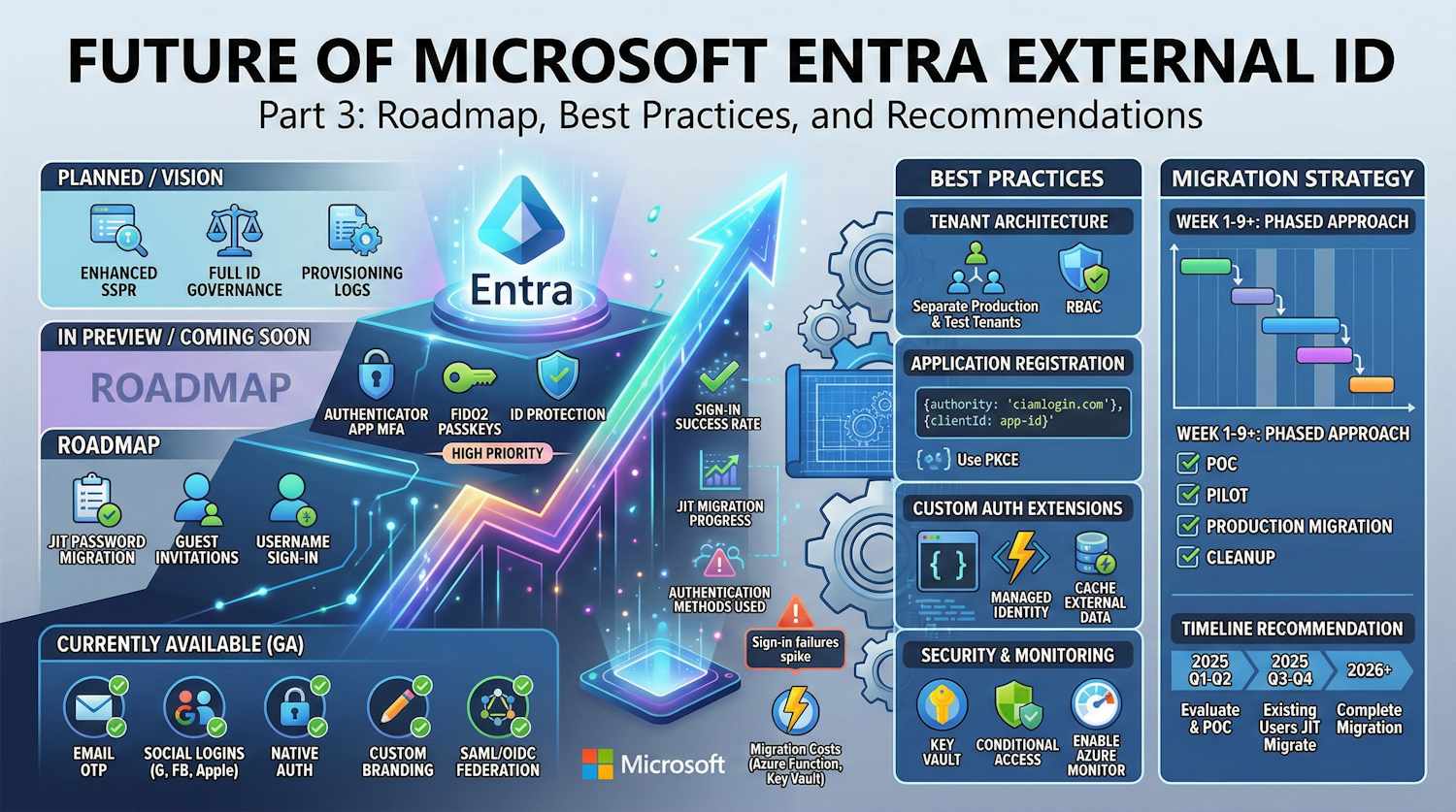
This final post in the series covers what's on the roadmap for External ID, how to set it up properly, and my take on when to actually migrate rather than wait.
External ID Roadmap
Currently Available (GA)
| Feature | Description |
|---|---|
| Email + Password | Standard consumer authentication |
| Email OTP | Passwordless email verification |
| Social Identity Providers | Google, Facebook, Apple, Microsoft Account |
| Native Authentication | Full UI control for mobile apps |
| Custom Authentication Extensions | Webhooks for custom logic |
| Company Branding | Full UI customization |
| Custom URL Domains | Your domain for sign-in pages |
| SAML/OIDC Federation | Enterprise identity provider support |
| Device Authorization Flow | OAuth 2.0 device code flow for input-constrained devices |
| Client Credentials (v2.0) | Daemon and service-to-service authentication |
In Preview
| Feature | Status | Notes |
|---|---|---|
| JIT Password Migration | Public Preview | Via Custom Authentication Extension |
| Guest Invitations | Preview | Admin-role invitations only, not for CIAM user flows |
| Azure Monitor Integration | Preview | One-click log export and monitoring |
| Username / Alias Sign-in | Public Preview | Sign in with custom identifier (e.g. membership ID) in addition to email |
Planned / Coming Soon
Based on B2C feature parity requirements and Microsoft announcements:
| Feature | Priority | Notes |
|---|---|---|
| Authenticator App MFA | High | Currently email/SMS only |
| FIDO2 Passkeys | High | Modern passwordless |
| ID Protection | High | Risk-based authentication |
| Full Groups Support | High | App roles being phased in |
| ID Governance | Medium | Access reviews, entitlements |
| Enhanced SSPR | Medium | More authentication methods |
| Provisioning Logs | Medium | User lifecycle tracking |
Migration Toolkit Roadmap
The B2C to External ID Migration Kit is evolving with planned features:
Currently Available
- Bulk user export from B2C
- Bulk user import to External ID
- JIT password migration via Custom Authentication Extension
- Attribute mapping and transformation
- Local development mode (Azurite)
- Application Insights telemetry
Planned Enhancements
| Feature | Description |
|---|---|
| Automated Infrastructure | Bicep/Terraform templates for deployment |
| SFI Compliance | Private Endpoints, VNet integration |
| Profile Synchronization | Bidirectional sync during coexistence |
| Managed Identity | Key Vault integration without secrets |
| Multi-Region Support | Geo-distributed migration |
Best Practices
1. Tenant Architecture
Recommendations:
- Separate tenants for production and dev/test
- Use workforce tenant for admin operations
- Implement proper RBAC across tenants
2. Application Registration
{
"app_settings": {
"authority": "https://yourtenant.ciamlogin.com/",
"client_id": "your-app-id",
"redirect_uris": [
"https://yourapp.com/auth/callback",
"https://jwt.ms"
]
}
}
Best Practices:
- Use
.ciamlogin.comauthority - Register separate apps for dev/test/prod
- Implement proper token validation
- Use PKCE for public clients
3. Custom Authentication Extensions
When using Custom Auth Extensions for claims enrichment or validation:
// Best practice: Use managed identity
var credential = new DefaultAzureCredential();
// Best practice: Cache external data
private static readonly MemoryCache _cache = new MemoryCache(new MemoryCacheOptions());
// Best practice: Implement retry logic
var retryPolicy = Policy
.Handle<HttpRequestException>()
.WaitAndRetryAsync(3, retryAttempt =>
TimeSpan.FromSeconds(Math.Pow(2, retryAttempt)));
4. Security Considerations
| Area | Recommendation |
|---|---|
| Secrets | Use Key Vault, never hardcode |
| Network | Private endpoints for production |
| Logging | Never log passwords or tokens |
| Certificates | Use Key Vault-generated, auto-rotate |
| Conditional Access | Require MFA for sensitive apps |
| Monitoring | Enable Azure Monitor, set up alerts |
5. Migration Strategy
Phased Approach:
Week 1-2: POC
├── Set up External ID tenant
├── Create test application
├── Test authentication flows
└── Validate JIT migration
Week 3-4: Pilot
├── Migrate 100-500 users
├── Monitor JIT function
├── Gather user feedback
└── Address issues
Week 5-8: Production Migration
├── Bulk migrate all users
├── Update application endpoints
├── Monitor closely
└── Support users
Week 9+: Cleanup
├── Verify all users migrated
├── Decommission B2C
└── Document lessons learned
When to Migrate
Migrate Now If:
- Building new consumer applications
- B2C custom policies are minimal
- Need Native Authentication for mobile
- Want unified Microsoft identity platform
- Have simple sign-up/sign-in flows
Wait If:
- Heavy investment in IEF custom policies
- Require ID Protection (risk-based auth)
- Need full ID Governance features
- Complex MFA requirements (FIDO2, Authenticator)
- Regulatory requirements need audit trail features not yet available
Timeline Recommendation
2025 Q1-Q2: Evaluate and POC
├── Test External ID features
├── Assess custom policy complexity
└── Plan migration approach
2025 Q3-Q4: Pilot and Production
├── Migrate new applications first
├── JIT migrate existing users
└── Monitor feature parity
2026+: Complete Migration
├── All new projects on External ID
├── Legacy B2C fully migrated
└── Decommission B2C
Cost Considerations
External ID Pricing
| Tier | MAU Limit | Price |
|---|---|---|
| Free | 50,000 | $0 |
| P1 | Unlimited | Per MAU |
| P2 | Unlimited | Per MAU |
Key Differences from B2C:
- Same MAU-based pricing model
- No separate MFA add-on required
- Premium features require P1/P2
- All users count (not just guests)
Migration Costs
| Component | Cost |
|---|---|
| Azure Function | ~$20-100/month (consumption) |
| Key Vault | ~$5-20/month |
| Blob Storage | ~$5-20/month |
| Development Time | 2-8 weeks |
Integration Patterns
Pattern 1: Direct Integration (Recommended)

Use MSAL libraries with External ID authority:
const msalConfig = {
auth: {
clientId: "your-app-id",
authority: "https://yourtenant.ciamlogin.com/",
redirectUri: "https://yourapp.com/auth/callback"
}
};
Pattern 2: Native Authentication (Mobile)

Full control over UI with SDK calls to External ID APIs.
Pattern 3: Claims Enrichment

Use TokenIssuanceStart event to add claims from external systems.
Monitoring and Operations
Key Metrics to Track
// Sign-in success rate
SigninLogs
| where TimeGenerated > ago(24h)
| where AppDisplayName == "Your Consumer App"
| summarize
Total = count(),
Success = countif(ResultType == 0),
Failure = countif(ResultType != 0)
| extend SuccessRate = round(100.0 * Success / Total, 2)
// JIT migration progress
// (Custom metric from your Function)
customMetrics
| where name == "JitMigrationSuccess"
| summarize MigratedToday = sum(value) by bin(timestamp, 1d)
// Authentication methods used
SigninLogs
| where TimeGenerated > ago(7d)
| summarize count() by AuthenticationMethodsUsed
Alerts to Configure
| Alert | Condition | Priority |
|---|---|---|
| Sign-in failures spike | >10% increase in failures | High |
| JIT function errors | Any 5xx response | Critical |
| Latency increase | P95 > 3 seconds | Medium |
| New user surge | >200% normal sign-ups | Low |
Summary and Recommendations
Bottom Line
B2C is end-of-sale for new customers, so if you're building something new, External ID is where you start. For existing B2C deployments, Microsoft's migration toolkit handles both bulk and JIT scenarios well. The platform still has gaps — ID Protection and FIDO2 aren't there yet — but they're clearly on the roadmap. If you wait for perfect feature parity, you'll keep waiting.
Action Items
| Priority | Action |
|---|---|
| Immediate | Evaluate External ID for new projects |
| Short-term | POC migration toolkit in dev environment |
| Medium-term | Pilot migration with subset of users |
| Long-term | Full production migration and B2C decommission |
Final Thoughts
External ID has come a long way in a short time. While some B2C features are still being ported over, what's there today is solid enough for most consumer sign-up/sign-in scenarios. If you're running B2C, here's where to focus:
- Start new projects on External ID
- Plan migrations for existing B2C applications
- Monitor Microsoft's roadmap for feature updates
- Invest in Custom Authentication Extensions for flexibility
The migration toolkit, especially JIT password migration, makes the transition smooth for end users while providing a structured approach for IT teams.
Resources
Documentation
Tools
Community
← Part 2 - Migration Tools | ← Part 1 - Introduction
This concludes the Microsoft Entra External ID series. For questions or assistance with your migration, contact your Microsoft representative or visit the resources above.