🔐 The Modern Data Governance Challenge
Organizations today face a perfect storm of data security and compliance challenges:
- Fragmented Security Tools: Data protection is scattered across multiple point solutions—DLP tools, classification systems, insider risk platforms, eDiscovery tools—none of which see the complete picture
- Compliance Complexity: Meeting requirements across GDPR, HIPAA, SOC 2, ISO 27001, and industry-specific regulations while operating in multiple regions and business units
- User Experience vs. Security: Protecting sensitive data without creating friction that drives users to shadow IT and unsanctioned tools
- Skill Shortage: Organizations lack enough cybersecurity professionals to manage increasingly complex security environments
- Emerging AI Risks: New threats from agentic AI applications that autonomously access and process sensitive data
- Exploding Data Volume: Cloud adoption, remote work, and digital transformation have created data sprawl that's impossible to manage with traditional approaches
Microsoft Ignite 2025 announcements reveal how Microsoft Purview is evolving to address these challenges with AI-powered capabilities that centralize visibility, automate risk management, and protect data in new ways—including safeguarding AI agents themselves.
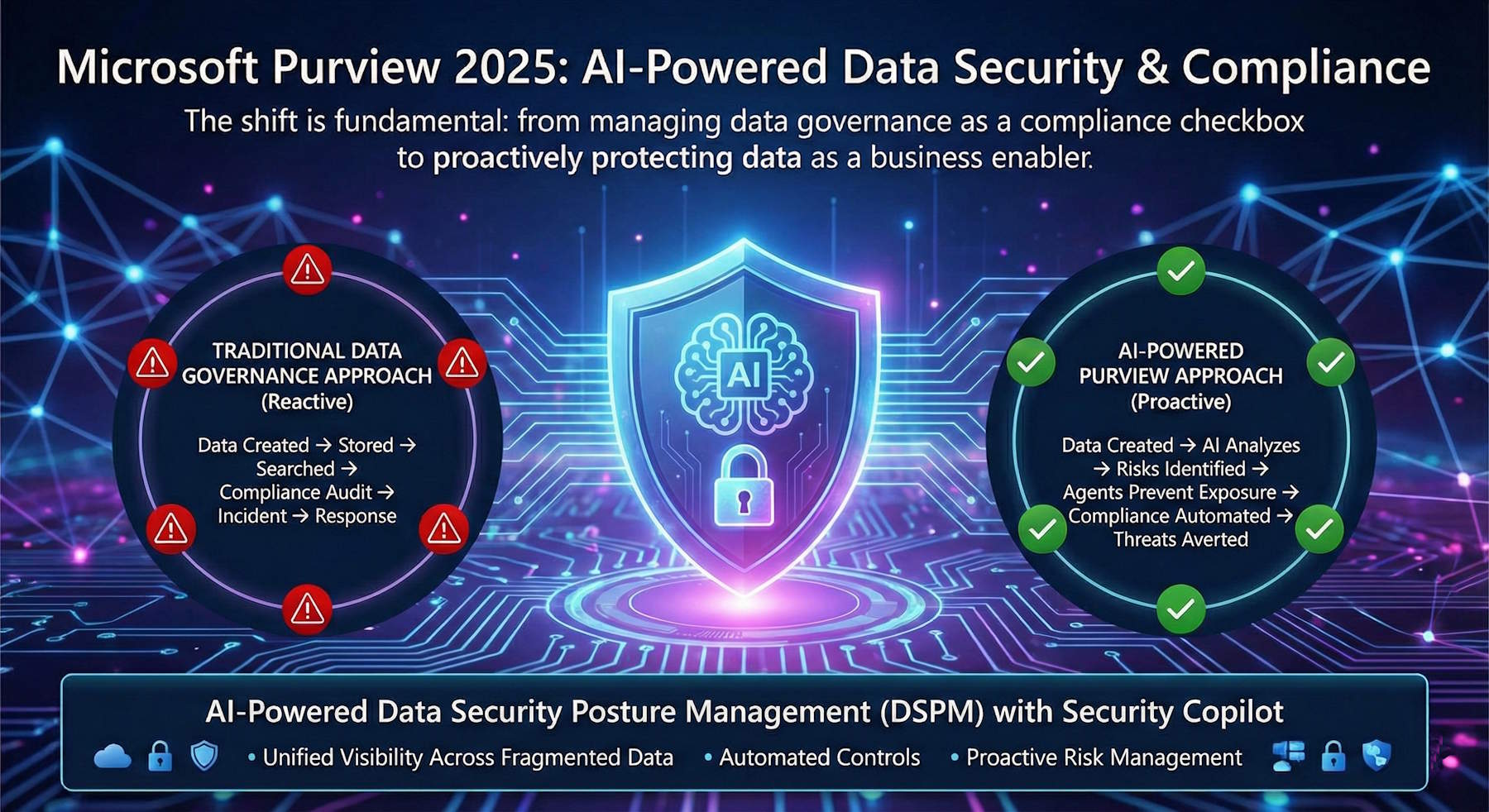
The Evolution: From Reactive to Proactive Data Governance
Traditional Data Governance Approach
graph LR
A[Data Created] --> B[Stored]
B --> C[Searched]
C --> D[Compliance Audit]
D --> E[Incident]
E --> F[Response]
style A fill:#ffcccc
style F fill:#ffcccc
classDef reactive fill:#ffcccc,stroke:#ff0000,stroke-width:2px
Characteristics: Reactive, slow, after damage is done
AI-Powered Purview Approach
graph LR
A[Data Created] --> B[AI Analyzes
Real-Time]
B --> C[Risks Identified
Proactively]
C --> D[Agents Prevent
Exposure]
D --> E[Compliance
Automated]
E --> F[Threats
Averted]
style A fill:#ccffcc
style B fill:#ccffcc
style C fill:#ccffcc
style D fill:#ccffcc
style E fill:#ccffcc
style F fill:#ccffcc
classDef proactive fill:#ccffcc,stroke:#00aa00,stroke-width:2px
Characteristics: Proactive, continuous, AI-driven, prevents problems
The shift is fundamental: from managing data governance as a compliance checkbox to proactively protecting data as a business enabler.
Innovation 1: AI-Powered Data Security Posture Management (DSPM)
What is DSPM?
Data Security Posture Management is the continuous assessment of an organization's data security state across all:
- Data repositories (databases, data lakes, file shares, cloud storage)
- Data flows (between systems, to third parties, to AI models)
- Data access patterns (who accesses what, when, and from where)
- Data protection controls (encryption, classification, access controls)
DSPM answers critical questions:
- Where is all our sensitive data located?
- Who has access to sensitive data, and should they?
- Is sensitive data properly encrypted and classified?
- Are there unauthorized access attempts or anomalies?
- Are we compliant with regulations requiring data protection?
The Problem: Traditional DSPM Limitations
Existing DSPM tools suffer from significant gaps:
| Challenge | Impact |
|---|---|
| Limited visibility | Only see data in connected repositories; miss data in cloud apps, shadow IT, vendor systems |
| Fragmented controls | DLP in Microsoft 365, different controls in AWS, different approach for Salesforce |
| Manual policies | Security teams manually write rules; hard to keep up with new data types and regulations |
| No context | Can't distinguish between legitimate business access and actual risk |
| Reactive alerts | Wait for exposure to happen, then respond (too late for damage control) |
| Skill intensive | Requires expert security architects to configure and maintain |
The Solution: AI-Powered DSPM with Security Copilot
Microsoft Purview's enhanced DSPM (in preview) uses AI and agentic capabilities to overcome these limitations:
1. Unified Visibility Across Fragmented Data
The Capability: Single pane of glass showing sensitive data across:
- Microsoft 365 (SharePoint, Exchange, Teams)
- Azure (SQL Database, Cosmos DB, Data Lake, Storage Accounts)
- AWS (S3 buckets, RDS, DynamoDB)
- Google Cloud (Cloud Storage, BigTable, Firestore)
- SaaS applications (Salesforce, Workday, ServiceNow, etc.)
- On-premises systems (file shares, databases, legacy apps)
- Third-party and vendor systems
How it Works:
graph TD
A[Data Repositories] --> B[AI-Powered Discovery]
B --> C[Content Analysis
ML Classification]
C --> D[Context Enrichment
Business Context]
D --> E[Risk Scoring]
B1[Azure] --> B
B2[AWS] --> B
B3[M365] --> B
B4[SaaS] --> B
B5[On-Prem] --> B
C --> C1[PII Detected]
C --> C2[Financial Data]
C --> C3[Health Records]
C --> C4[Trade Secrets]
D --> D1[Owner/Department]
D --> D2[Data Criticality]
E --> E1[Sensitivity Level]
E --> E2[Access Patterns]
E --> E3[Exposure Risk]
E --> E4[Compliance Requirements]
style B fill:#e1f5ff
style C fill:#fff4e1
style D fill:#ffe1f5
style E fill:#f5e1ff
Real-World Scenario: A financial services organization has customer credit card data stored in:
- SQL database in Azure (operational system)
- S3 bucket in AWS (backup and analytics)
- Salesforce instance (sales team access for customer interactions)
- SharePoint folder (shared with compliance team)
- Vendor's system (third-party payment processor)
Traditional DSPM tools see these as disconnected silos. AI-powered Purview sees this as one data asset with five exposure points, correlates risk across all of them, and alerts on the highest-risk configuration.
2. Agentic DSPM That Works Like Your Security Team
The Capability: AI agents that act like experienced security architects, automatically:
- Discovering sensitive data without human intervention
- Assessing posture gaps (controls that should be in place but aren't)
- Recommending improvements specific to the organization's data and business
- Suggesting policy refinements as new data types emerge or business needs change
Security Copilot Integration: All DSPM insights are fed into Security Copilot, enabling natural language queries:
- "Show me all customer data that's not encrypted"
- "Which employees have access to more sensitive data than their role requires?"
- "What's our GDPR compliance status across all repositories?"
- "Which third-party vendor access poses the highest risk?"
Real-World Scenario: A healthcare organization recently acquired another company with different systems and security practices.
flowchart TD
A[Healthcare Acquisition] --> B[DSPM Agent Scans]
B --> C[Discovery Phase]
C --> C1[Weak Encryption
Patient Database]
C --> C2[Too Many
Admin Users]
C --> C3[Incomplete
Audit Logs]
C1 --> D[Assessment]
C2 --> D
C3 --> D
D --> E[HIPAA Violation
Analysis]
E --> F[Risk Correlation]
F --> G[Recommendations]
G --> G1[Enable AES-256
Encryption]
G --> G2[Implement RBAC
5 Admin Max]
G --> G3[Enable Full
Audit Logging]
G1 --> H[Priority Ranking]
G2 --> H
G3 --> H
H --> I[Security Team
Reviews]
I --> J[One-Click
Approval]
J --> K[Automated
Implementation]
style C1 fill:#ffcccc
style C2 fill:#ffcccc
style C3 fill:#ffcccc
style E fill:#ffffcc
style K fill:#ccffcc
L[Time Saved:
Weeks → Hours]
style L fill:#e1f5ff
Human security team reviews recommendations and approves implementation with a single click rather than spending weeks on manual assessment.
3. Combining Internal Signals with External Threat Intelligence
The Capability: DSPM that incorporates:
- Internal signals: Access patterns, data flows, policy violations, unusual behavior
- External signals: Threat intelligence, known vulnerability indicators, breach data feeds, third-party risk assessments
- Agentic activities: AI agents accessing data, LLM usage patterns, model grounding behavior
Real-World Scenario: A manufacturer discovers its product design data is accessible from multiple cloud apps. DSPM correlates:
- Internal signal: Unusual file access from a sales employee at 2 AM
- External signal: Threat intelligence indicates state-sponsored IP address accessing systems in similar industry
- Agentic signal: An LLM agent configured for competitive analysis is accessing design documents as grounding data
- Correlation: High-risk situation combining potential data theft (unusual access) with known threat actor interest (external signal) and unintended AI data exposure
Traditional DSPM would catch unusual access. Purview adds the threat context and AI safety dimension, enabling smarter decision-making.
Innovation 2: Data Security for AI Agents
The Agentic AI Risk Space
As organizations deploy AI agents: autonomous applications that take actions without human approval—new data security risks emerge:
New Data Security Risks with Agents
- Unintended Data Grounding: AI agent configured to answer customer questions uses sensitive employee data as grounding information
- Data Leakage Through Responses: Agent returns information containing sensitive data in its response to user queries
- Compliance Violations: Agent accesses data in violation of compliance requirements (e.g., GDPR data localization)
- Unauthorized Access: Agent accesses data outside its intended scope using granted permissions
- Third-Party Data Exposure: Agent sends data to third-party AI services without proper controls
- Supply Chain Risk: Compromised agent plugin leaks sensitive data
Traditional Controls Don't Work
- DLP tools don't see what happens inside LLM models
- Access controls can't distinguish between user accessing data and AI agent using data for grounding
- Encryption doesn't work for data that needs to be analyzed by AI
- Classification systems don't track data flowing through AI agents
- Insider risk tools don't understand agentic vs. human behavior
The Solution: Agent-Focused Data Security Capabilities
Microsoft Purview for Agents (in preview) adds new capabilities specifically designed for agentic AI:
1. Agent-Specific Risk Detections
New detection types that understand agentic AI behavior:
- Unauthorized Data Access via Agent: Detects when agents access data outside their configured scope
- Sensitive Data in Agent Responses: Identifies when agent responses contain sensitive data that shouldn't be exposed
- Compliance Violation by Agent: Detects agents violating data residency, processing, or retention requirements
- Unusual Agent Data Flow: Identifies abnormal patterns in data accessed or processed by agents
- Agent-to-Third-Party Data Transfer: Tracks when agents send data to external services (including third-party AI APIs)
- Compromised Agent Plugin: Detects suspicious behavior from agent plugins or tools
2. Extended Visibility and Control
New capabilities for monitoring and controlling agent behavior:
- Agent Data Audit Trail: Complete log of what data each agent accessed, when, and why
- Real-Time Agent Monitoring: Dashboard showing current agent activities and data flows
- Agent Data Lineage: Understand how data flows through agent chains (Agent A passes data to Agent B)
- Granular Agent Permissions: Restrict agent access to specific data categories or sensitivity levels
- Agent Response Inspection: Review and audit responses agents generate, including data they contain
3. Proactive Risk Analysis
AI-powered risk analysis specific to agents:
- Attack Path Analysis for Agents: Show how a compromised or misconfigured agent could expose data
- Data Exposure Modeling: Predict what sensitive data would be exposed if agent is compromised
- Least Privilege Recommendations: Suggest minimal data access required for agent to function
- Compliance Impact Assessment: Show which regulations are affected by current agent configuration
Real-World Scenario: A company deploys an HR agent that answers employee questions about benefits, compensation, and leave policies. The agent is granted access to the HR database containing:
- Employee names and IDs
- Salary information
- Health insurance details
- Tax information
- Disciplinary records
Purview detects that:
- Risk: Agent can access salary and disciplinary records but shouldn't (users asking about benefits shouldn't get this data)
- Compliance Impact: Exposure of employee health information violates HIPAA and GDPR
- Data Flow: When agent generates responses containing employee names + compensation, this could be exposed to users outside HR
- Recommendation: Restrict agent to only benefits and leave data; mask employee IDs; prevent compensation/disciplinary data in responses
The organization implements these changes, agent continues providing value while risk drops significantly.
Innovation 3: Enhanced DLP for Microsoft 365 Copilot and AI Agents
The Problem: AI Breaks Traditional Data Loss Prevention
Traditional DLP works by inspecting:
- Email attachments before sending
- File downloads before accessing
- API calls before data leaves the system
But AI changes the equation:
- Copilot prompts aren't typically blocked by traditional DLP
- Information in prompts becomes part of model training or grounding
- Responses from Copilot might contain sensitive data
- Agents access data through APIs that don't pass through traditional DLP inspection points
The Solution: Real-Time Copilot and Agent DLP Controls
New DLP capabilities (in preview) specifically for AI:
1. Real-Time Prompt Inspection
Capability: Inspect prompts in real-time before they're sent to Copilot or AI agents:
- Sensitive Data Detection: Identify when prompts contain PII, credentials, financial data, health information, etc.
- Policy Enforcement: Block prompts containing sensitive data OR redact sensitive portions before sending
- Compliance Controls: Prevent prompts violating specific regulations (e.g., GDPR right to be forgotten)
How it works:
flowchart TD
A[User Composes Prompt] --> B[Purview DLP Scans]
B --> C{Policy Violation?}
C -->|Yes| D{Severity Level}
C -->|No| E[Send to Copilot]
D -->|High Risk| F[Block Prompt]
D -->|Medium Risk| G[Auto-Redact Sensitive Data]
D -->|Critical| H[Alert Admin]
F --> F1[Explain to User
Suggest Alternatives]
G --> G1[Show Modified Prompt
User Approves]
H --> H1[Log Security Event]
G1 --> E
E --> I[AI Processing]
I --> J[Return Response]
style B fill:#e1f5ff
style C fill:#fff4e1
style D fill:#ffe1f5
style F fill:#ffcccc
style G fill:#ffffcc
style H fill:#ffcccc
2. Response Inspection and Control
Capability: Inspect Copilot responses for sensitive data before returning to user:
- Sensitive Data in Responses: Detect when responses contain PII, health data, credentials, etc.
- Grounding Data Exposure: Identify when responses expose data used for model grounding
- Blocking Rules: Prevent responses containing sensitive data from being returned
- User Notification: Explain why response is blocked and suggest alternative phrasing
3. Agent Data Handling Rules
Capability: Define policies for how agents can use sensitive data:
- Grounding Restrictions: Prevent agents from using certain data types for grounding (e.g., "Don't use customer PII for HR agent grounding")
- Response Sanitization: Remove sensitive data from agent responses automatically
- Data Minimization: Agents only access minimum data needed to answer query
- Routing Rules: Prevent agents from forwarding sensitive data to specific destinations
Real-World Scenario: A customer service agent handles incoming tickets. User asks: "Why is my order delayed? My order number is #12345 and my credit card ending in 4567 is on file."
flowchart LR
subgraph Without["Without DLP for Agents"]
W1[User Query
Order #12345
Card: 4567] --> W2[Agent Processes
Full Prompt]
W2 --> W3[Query Database
with Card Info]
W3 --> W4[Response Contains
Card Number]
W4 --> W5[Data Exposed
Logs/Training]
style W5 fill:#ffcccc
end
subgraph With["With DLP for Agents"]
D1[User Query
Order #12345
Card: 4567] --> D2[DLP Scans]
D2 --> D3{Card Number
Detected?}
D3 -->|Yes| D4[Redact Card Info]
D4 --> D5[Agent Processes
Order #12345 Only]
D5 --> D6[Query Database
No Card Info]
D6 --> D7[Safe Response
No Sensitive Data]
style D7 fill:#ccffcc
end
Without DLP: Credit card information flows through agent processing, appears in responses, logs, and potentially training data.
With DLP: Sensitive payment information is detected and redacted before processing, protecting data while still providing useful response.
Innovation 4: Security Copilot Agents for Data Security
Agent 1: Data Security Posture Agent (Preview)
Purpose: Proactively discover sensitive data, assess gaps, and improve policy hygiene
Capabilities:
- Automated Discovery: Continuously scan all data repositories for sensitive content
- Posture Assessment: Evaluate current controls against industry best practices and regulatory requirements
- Gap Analysis: Identify what should be in place but isn't
- Policy Recommendations: Suggest specific policy changes with implementation steps
- Improvement Tracking: Monitor progress as policies are implemented
How it helps security admins:
Instead of: "We need to audit all our data repositories, manually assess encryption, evaluate access controls, compare against GDPR/HIPAA/SOC2 requirements, and create a remediation plan"
With the agent: Describe your data environment and compliance requirements, the agent automatically discovers all sensitive data, compares against requirements, recommends improvements, and tracks implementation.
Real-World Scenario: A mid-sized SaaS company with compliance certification requirements:
- Admin question: "Are we compliant with SOC 2 Type II data handling requirements?"
- Agent discovers: 847 GB of customer data spread across 12 cloud storage locations, 3 databases, various backups
- Agent assesses: Compares current controls against SOC 2 requirements
- Agent identifies gaps:
- 340 GB of customer data not encrypted at rest (violates SOC 2 requirement #5)
- Backup retention policy allows 1-year retention (exceeds SOC 2 requirement of 90 days)
- Database access logs incomplete (violates audit requirement)
- Agent recommends:
- Enable encryption at rest for all customer data repositories (estimated 4 hours work)
- Update backup retention policy (5 minutes)
- Enable comprehensive database audit logging (2 hours)
- Admin executes: Implements recommendations with full tracking
- Agent verification: Confirms compliance after changes
Time saved: What would take a compliance analyst 40+ hours is accomplished in interactive session with agent guidance.
Agent 2: Data Security Alert Triage Agent (Generally Available)
Purpose: Triage, prioritize, and remediate security alerts automatically
Capabilities:
- Alert Ingestion: Receives security alerts from Purview, Defender, and other sources
- Correlation: Groups related alerts into incidents
- Context Enrichment: Adds business context to alerts (data sensitivity, business impact, user risk)
- Prioritization: Ranks alerts by actual risk to organization
- Automated Response: Takes automatic response actions for low-risk/high-confidence alerts
- Alert Recommendation: Suggests remediation for high-risk alerts
How it helps security analysts:
Instead of: "We have 500+ alerts from yesterday. Which ones are actually critical? What should we prioritize?"
With the agent: "Automatically triage all alerts, show me the top 10 that require attention, suggest immediate actions for others"
Alert Prioritization Examples:
| Alert | Raw Priority | Context | New Priority | Action |
|---|---|---|---|---|
| 1000 failed login attempts from IP X | High | IP from known datacenter (VPN provider), failed attempts to test account | Low | Auto-resolve, no action |
| Employee downloaded 100 GB file at 2 AM | High | Employee in India (timezone appropriate), monthly data extract job scheduled for this time | Low | Auto-resolve with note |
| Sensitive file shared with external domain | Critical | File contains customer PII, domain is recently registered, no business relationship | Critical | Require immediate admin review |
| Unusual Copilot data access by agent | Medium | Agent configured to access this data, access pattern normal for agent, data within agent scope | Low | Auto-resolve |
Real-World Scenario: Security team receives 847 alerts overnight:
flowchart TD
A[847 Alerts Overnight] --> B[Alert Triage Agent]
B --> C[Correlation Engine]
C --> D1[240 Alerts
Password Spray]
C --> D2[180 Alerts
Backup Scripts]
C --> D3[3 Alerts
Insider Threat]
C --> D4[424 Alerts
Other Noise]
D1 --> E1{Priority:
HIGH}
D2 --> E2{Priority:
LOW}
D3 --> E3{Priority:
CRITICAL}
D4 --> E4{Priority:
LOW}
E1 --> F1[Auto-Block
5 Botnet IPs]
E2 --> F2[Auto-Resolve
Known Pattern]
E3 --> F3[Escalate to
Human Analyst]
E4 --> F4[Auto-Dismiss]
F1 --> G[Automated Actions]
F2 --> G
F4 --> G
F3 --> H[Security Analyst
Reviews 3 Alerts]
G --> I[400+ Alerts
Auto-Resolved]
H --> J[Focus on
Real Threats]
style A fill:#ffcccc
style E3 fill:#ff6666
style F3 fill:#ff6666
style H fill:#ffffcc
style I fill:#ccffcc
style J fill:#ccffcc
K[Result: 847 → 3 Alerts
99.6% Reduction]
style K fill:#e1f5ff
Team can focus on real threats instead of drowning in noise.
Implementation Architecture: How It All Works Together
graph TB
subgraph DataSources["Data Sources"]
DS1[Azure]
DS2[AWS]
DS3[M365]
DS4[SaaS]
DS5[On-Prem]
end
subgraph PurviewEngine["Microsoft Purview Data Engine"]
PE1[AI-Powered Discovery]
PE2[Classification]
PE3[Analysis]
end
subgraph DSPM["Data Security Posture Management"]
D1[Risk Scoring]
D2[Compliance Checking]
D3[Gap Analysis]
end
subgraph AgentControls["Agent-Specific Controls"]
AC1[Agent Risk Detection]
AC2[Data Grounding Restrictions]
end
subgraph DLP["DLP Enforcement"]
DLP1[Email/File DLP
Traditional]
DLP2[Copilot Prompt/Response DLP
New]
DLP3[Agent Data Handling DLP
New]
end
subgraph Copilot["Security Copilot"]
SC1[Data Security Posture Agent
Recommendations]
SC2[Alert Triage Agent
Prioritization]
end
Dashboard[Security Team Dashboard & Actions]
DataSources -->|APIs, Connectors| PurviewEngine
PurviewEngine --> DSPM
DSPM --> AgentControls
AgentControls --> DLP
DLP --> Copilot
Copilot -->|Unified Interface| Dashboard
style PurviewEngine fill:#e1f5ff
style DSPM fill:#fff4e1
style AgentControls fill:#ffe1f5
style DLP fill:#f5e1ff
style Copilot fill:#e1ffe1
style Dashboard fill:#ffe1e1
Key Features Summary
1. Unified Visibility
- Single pane of glass for all sensitive data across cloud, on-premises, SaaS
- Automated discovery of sensitive content without manual configuration
- Business context enrichment (owner, department, data criticality)
- Risk scoring based on sensitivity + exposure + compliance requirements
2. AI-Powered Risk Management
- Automated posture assessment comparing current state to best practices and regulations
- Proactive recommendations from agents acting like security architects
- Policy automation that improves over time as data changes
- Natural language queries through Security Copilot interface
3. Agent-Safe Data Security
- Agent-specific detections for risks unique to agentic AI
- Prompt and response inspection for AI tools
- Grounding data restrictions to prevent unintended data exposure
- Agent audit trails for compliance and investigation
4. Intelligent Alert Management
- Alert correlation grouping related alerts into meaningful incidents
- Risk-based prioritization focusing on what actually matters
- Automated response for low-risk, high-confidence alerts
- Analyst productivity improvement by eliminating alert noise
Best Practices for Data Governance at Scale
1. Data Classification as Foundation
- Establish taxonomy: Define sensitivity levels (public, internal, confidential, restricted)
- Automated classification: Use AI to classify data as it's created
- Regular review: Audit classification accuracy as business changes
- User education: Help users understand classification and why it matters
2. Zero Trust for Data
- Principle of least privilege: Every user/agent gets minimum access needed
- Continuous verification: Verify access is still appropriate periodically
- Micro-segmentation: Isolate sensitive data from general network
- Encryption everywhere: Encrypt sensitive data at rest and in transit
3. Compliance as Code
- Policy templates: Use predefined policies for common regulations (GDPR, HIPAA, SOC 2)
- Continuous compliance: Automated checking vs. requirements
- Audit automation: Generate compliance reports automatically
- Evidence collection: Gather logs for regulatory audits automatically
4. Human-Centered Security
- Enable users: Make security easy so users follow guidelines
- Minimize friction: Reduce false positives and blocking of legitimate work
- Transparency: Explain why security controls are in place
- Training: Educate employees about data risks and their role in protection
5. AI Safety by Design
- Inventory agents: Document all AI applications and their data access
- Assess risks: Use Purview to identify potential exposures
- Least privilege for agents: Restrict agent access to necessary data
- Monitoring: Continuously audit agent behavior for anomalies
Real-World Implementation Scenarios
Scenario 1: Financial Services Regulatory Compliance
Organization: Mid-size investment firm (500 employees)
Challenge:
- Subject to SEC, FINRA, SOX, SOC 2 compliance
- Data spread across 15+ systems
- Manual compliance audits taking 2 weeks per quarter
- Recent data exposure when employee accidentally shared client portfolios
Solution:
- DSPM deployment: Unified visibility across all client data
- Automated discovery: AI identifies where client PII and financial data reside
- Compliance mapping: Purview compares current controls to SOX/FINRA/SEC requirements
- Gap remediation: Implement encryption, access controls, audit logging per recommendations
- Alert management: Triage agent reduces compliance alerts from 500+ to <10 per week requiring attention
Results:
- Compliance audit preparation time reduced from 10 days to 2 days
- Data exposure risk reduced by 87% within 3 months
- Regulatory confidence improved (last audit: zero findings vs. prior audit: 5 findings)
Scenario 2: Healthcare HIPAA Compliance
Organization: Health system with 20 hospitals, 5,000 employees
Challenge:
- Subject to strict HIPAA regulations
- Patient data in EHR systems, but also in:
- Email discussions about patient care
- Shared drives for research
- Third-party healthcare analytics vendors
- New AI agents analyzing patient outcomes
- HIPAA violations can result in $100+ million in fines
Solution:
- Healthcare-specific DSPM: Configure Purview for HIPAA requirements
- Sensitive data discovery: AI identifies all PHI (Protected Health Information)
- Agent security: Configure controls so clinical analytics agents can't expose patient names/IDs
- DLP for communications: Prevent accidental email leakage of patient data
- Vendor security: Audit which vendors access patient data and implement appropriate controls
Results:
- 100% of patient data now has appropriate access controls
- Email-based HIPAA violations dropped from 8/month to 0
- Third-party vendor risk fully visible and managed
- AI agents operate safely within HIPAA constraints
Scenario 3: SaaS Company with Multi-Cloud Data
Organization: B2B SaaS platform, 200 employees, customers in 40 countries
Challenge:
- Customer data in Azure (primary), AWS (analytics), and Google Cloud (backup)
- GDPR, CCPA, and regional data localization requirements
- Recently launched data analytics AI agents
- Pressure to automate security while maintaining compliance
Solution:
- Multi-cloud DSPM: Unified visibility across all cloud providers
- Compliance mapping: Different regions require different controls (GDPR, CCPA, etc.)
- Agent protection: Ensure analytics agents respect data residency requirements
- Automated compliance: Continuous verification that regional data stays in correct regions
- Alert automation: Triage agent immediately alerts on any cross-region data movement
Results:
- Compliance coverage expanded to all regions without expanding security team
- Zero compliance violations in annual audit (vs. 3 violations prior year)
- Launch of data agents without compliance risk
- Confidence to expand to additional regions
Addressing Common Concerns
"Won't these controls slow down our business?"
No, well-designed controls enable business agility:
- Automated classification means data is ready for compliance immediately
- Least privilege prevents accidental exposure while enabling legitimate work
- Alert automation means analysts focus on real risks, not noise
- Policy templates mean compliance is built in, not bolted on
"What about user privacy and surveillance concerns?"
Purview is designed with privacy in mind:
- Content never stored: Analysis happens on data in place; content doesn't move to Purview
- Aggregation and anonymization: Reports show trends, not individual details
- User transparency: Organizations should communicate how data is monitored
- Audit trails: All monitoring activity is logged for transparency
- Regulatory alignment: Purview respects privacy requirements like right to be forgotten
"How much will this cost?"
Significant ROI through:
- Reduced compliance effort: Hours saved on manual audits
- Prevented breaches: Reduced risk of costly data exposures
- Operational efficiency: Alert automation and policy recommendations reduce manual work
- Regulatory confidence: Reduced risk of fines from compliance violations
"We're not large enough to need this"
DSPM benefits organizations of any size:
- Small orgs: Automation means small security team can manage complex compliance
- Mid-market: Multi-cloud and AI introduce complexity that DSPM is designed for
- Enterprise: DSPM scales to massive data volumes and complex requirements
The Future of Data Governance
Microsoft Purview's 2025 enhancements represent a fundamental shift in how organizations approach data security:
- From reactive to proactive: Discover risks before they become incidents
- From manual to automated: AI agents handle routine tasks; humans focus on decisions
- From fragmented to unified: One platform for all data security and compliance needs
- From human-limited to scalable: Do more with smaller security teams through automation
Summary
- DSPM is now table stakes: In 2025, organizations need unified visibility across all data
- AI changes everything: Agentic AI introduces new risks that require new controls
- Compliance can be automated: From reactive audits to continuous automated compliance
- Agents amplify security team: Security Copilot agents multiply security team effectiveness
- Data governance enables business: Well-designed controls support business objectives, not just security
Resources
- Microsoft Ignite 2025 Book of News: https://news.microsoft.com/ignite-2025-book-of-news/
- Microsoft Purview Documentation: https://learn.microsoft.com/en-us/purview/
- Data Security Posture Management (DSPM): https://learn.microsoft.com/en-us/purview/purview-data-security-posture-management
- Data Loss Prevention (DLP): https://learn.microsoft.com/en-us/purview/dlp-learn-about-dlp
- Information Protection: https://learn.microsoft.com/en-us/purview/information-protection
- Insider Risk Management: https://learn.microsoft.com/en-us/purview/insider-risk-management
- Security Copilot Integration: https://learn.microsoft.com/en-us/security-copilot/
Ready to transform your data governance? Start with Microsoft Purview's DSPM capabilities to gain visibility into your data environment, then expand to agent protection as you deploy more autonomous AI applications. Your security team will thank you for the automation, your compliance officers will appreciate the continuous monitoring, and your organization will operate with dramatically reduced data risk.
The future of enterprise data security is intelligent, automated, and proactive. Purview makes it possible.