Unified Security Portal: Microsoft Defender for Cloud Meets GitHub Advanced Security
🔒 Development at Scale: The Security Challenge
The pace of development has scaled dramatically. Organizations now build more than 500 new applications on average each year – and as code volume grows, the gap between development and security widens. Historically, this meant tools scattered across Azure portal, GitHub dashboards, security consoles, and separate dashboards. Now? Everything is converging.
The fundamental problem: Working in separate tools with no shared context, developers can't see which threats security teams prioritize, and security teams can't easily trace issues back to their source in code. This creates a dangerous blind spot where vulnerabilities are discovered too late or never connected to their origins.
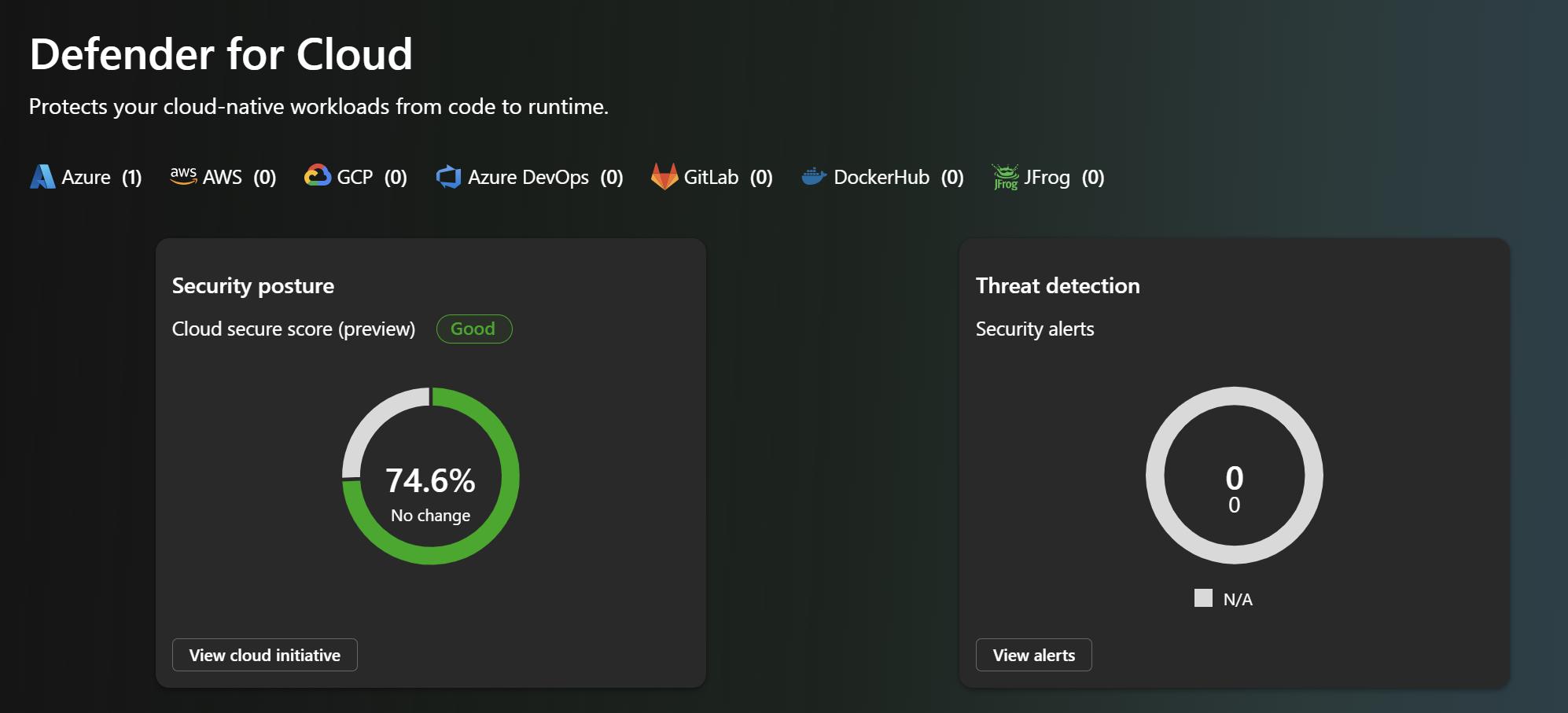
Microsoft Ignite 2025 announcement: Microsoft Defender for Cloud now natively integrates with GitHub Advanced Security (in public preview) – the first native link between runtime intelligence and developer workflows, delivering continuous protection from code to runtime. This bidirectional integration brings Defender for Cloud's runtime insights directly into GitHub, so vulnerabilities can be surfaced, prioritized, and remediated with AI assistance – all within the developer environment.
But here's what's even bigger: Defender for Cloud is now available in the unified Microsoft Defender security portal. This means GitHub organizations can be monitored and managed alongside your cloud infrastructure, all from one security dashboard. During the preview, initial GitHub setup still happens in Azure, but the unified experience is here. And Microsoft is rapidly moving toward complete feature parity, eventually putting all configuration and management in the unified portal too.
We start where every application does: in the code – and with a major step forward in how security and development teams work together.
Understanding the Problem: Why Code-to-Runtime Security Matters
Software supply chain attacks have become increasingly sophisticated, targeting the weakest links in the development pipeline. Traditional security approaches that focus on either code-time or runtime protection leave critical gaps in coverage. The rising tide of compromised dependencies, malicious commits, and runtime exploits demands a more comprehensive approach.
The Software Supply Chain Attack Surface
Recent years have seen explosive growth in supply chain attacks:
- Compromised Dependencies: Attackers inject malicious code into popular open-source packages used by thousands of projects
- Build Pipeline Exploitation: Compromised build systems can inject backdoors during the compilation process
- Runtime Exploitation: Vulnerabilities in production environments are exploited after deployment
- Lateral Movement: Once inside, attackers use runtime context to pivot to critical assets
Traditional point solutions address only part of this problem:
- Code scanning identifies vulnerabilities in source code but can't determine if they're actually exploitable in production
- Runtime monitoring detects malicious behavior but can't trace issues back to their source in code
- Dependency scanning finds vulnerable packages but lacks context about whether specific vulnerabilities are reachable or exploitable
The Developer-Security Team Disconnect
Another critical challenge is the disconnect between developers who build applications and security teams who protect them:
- Different Tools: Developers work in GitHub; security teams use Defender for Cloud
- Silos: Security findings often don't reach developers until late in the development cycle
- Context Loss: Security alerts lack business context, making prioritization difficult
- Slow Remediation: Without automated workflows, issues languish unfixed
The Solution: Unified Code-to-Runtime Security
The native integration between Microsoft Defender for Cloud and GitHub Advanced Security eliminates these gaps by:
- Connecting two critical security perspectives: Runtime threat intelligence informs code-level prioritization
- Enabling real-time collaboration: Direct integration between security and development teams
- Providing AI-powered remediation: Automatic fix suggestions accelerate resolution
- Establishing complete traceability: Track artifacts and threats from code through to runtime
How It Works
When Defender for Cloud detects a critical vulnerability in a running workload, developers see exactly where the issue originated in code, how it manifests in production, and suggestions for how to fix the vulnerability. With Copilot Autofix and GitHub Copilot coding agent capabilities, AI-generated and validated fixes are suggested in real time – shortening remediation cycles from days to hours.
Together, security, development, and AI now move as one, finding and fixing issues faster and creating a continuous feedback loop that learns from runtime, feeds insights back into development, and changes how secure apps and agents get built in the age of AI.
Three Tangible Benefits for Organizations
1. Collaborate Without Friction
The Benefit: Security teams can open and track GitHub issues directly from Defender for Cloud with context and vulnerability details, ensuring shared visibility between security and development.
What this means:
- No context lost in translation between tools
- Developers see security findings where they work
- Security teams maintain oversight of remediation progress
- Complete audit trail for compliance
Impact: Reduced time to triage and assignment, faster developer response
2. Accelerate Remediation with AI
The Benefit: Copilot-assisted fixes make it faster and safer to resolve vulnerabilities without breaking developer flow.
What this means:
- AI suggests secure code patterns automatically
- Developers don't need to research security best practices
- Generated fixes are tested and validated
- Security improvements without development delays
Impact: Remediation time reduced from days to hours
3. Prioritize What Matters Most
The Benefit: By mapping runtime threats directly to their source in code, teams can focus on vulnerabilities that are truly exploitable – not just theoretical.
What this means:
- Only focus on vulnerabilities with real business risk
- Reduce false positive fatigue
- Allocate developer time to high-impact work
- Maximize security improvement per engineering hour
Impact: 10x improvement in vulnerability triage efficiency
Three Major Features
1. Real-Time Visibility Across the App Lifecycle
The Challenge: Security and development teams work in isolation, seeing only partial visibility into application security. The Solution: Native integration creates a unified view of security across the entire application lifecycle:For Security Teams
- Open Issues Directly in GitHub: When a vulnerability is discovered in Defender for Cloud, security teams can create a GitHub issue directly from the security dashboard
- Security Campaign Alerts: Security teams can open targeted campaigns to notify GitHub repository owners about specific vulnerabilities
- Real-Time Status Tracking: Monitor the progress of vulnerability remediation as developers work on fixes
- Compliance Artifacts: Maintain an audit trail of discovered vulnerabilities, remediation efforts, and resolution
For Developer Teams
- Alerts in Their Workflow: Notifications appear in GitHub where developers already work, not in an external security tool
- Context and Guidance: Issues include detailed remediation suggestions and affected code references
- Collaboration Features: Developers and security teams can collaborate directly on fixes within GitHub
- Built-in Documentation: All remediation history and security decisions are documented in GitHub
Real-World Scenario: A security team detects a critically exploitable dependency vulnerability in a production application through Defender for Cloud's runtime analysis. Rather than sending a ticket through email or a separate system, they open a GitHub issue directly in the affected repository with priority labeling and assign it to the development team. Developers see the issue in their normal GitHub workflow and can immediately address it with full context about runtime exploitability.
2. Critical Alert Prioritization: From Code to Runtime Context
The Challenge: Security teams receive thousands of potential vulnerabilities. How do you know which ones actually matter?
The Solution: By connecting runtime context to code, organizations can prioritize based on actual exploitability:
Runtime Context as the Differentiator
The integration uses runtime data to answer critical questions:
- Is this vulnerability actually reachable? Code scanning might flag a vulnerable function, but if that function is never called in production, it's not exploitable
- Is there active exploitation? Runtime monitoring shows actual attack attempts targeting specific vulnerabilities
- What's the attack surface? Network traffic analysis reveals which systems can actually access vulnerable code
- What's the business impact? Runtime context shows which critical applications are affected
Attack Path Analysis
The integration maps attack paths that connect:
- Vulnerable code (identified by code scanning)
- Network exposure (identified by network monitoring)
- Active exploitation attempts (identified by threat detection)
- Lateral movement paths (identified by behavior analysis)
This comprehensive view means security teams can focus on the 5-10% of vulnerabilities that actually pose real risk, rather than drowning in noise from the other 95%.
Developer Prioritization
Developers see vulnerabilities ranked by:
- Exploitability: Can this actually be exploited in production?
- Active Threat: Are attackers currently attempting to exploit this?
- Business Impact: How critical are the affected systems?
- Fix Difficulty: How much effort is required to remediate?
Developers naturally focus on fixing the easy, high-impact issues first, maximizing security improvement per hour of development effort.
Real-World Scenario: A code scan identifies 500 potential vulnerabilities in a large codebase. Without runtime context, developers would need to review and remediate all 500. With runtime context from Defender for Cloud, the system identifies that only 23 of these vulnerabilities are actually reachable in production, 8 are actively being targeted by attackers, and 3 are critical for business systems. The team focuses on those 3 first, then works through the 8 actively attacked ones, then addresses other reachable vulnerabilities. This prioritization reduces remediation time from months to weeks.
3. AI-Powered Remediation: Fixing Issues Faster with Confidence
The Challenge: Understanding a vulnerability is one thing; fixing it correctly is another. Developers need guidance to implement secure fixes efficiently.
The Solution: GitHub Copilot and Microsoft AI capabilities provide automatic fix suggestions and guidance:
Copilot Autofix for Automatic Remediation
- Intelligent Code Generation: Copilot analyzes the vulnerable code and generates secure alternatives
- Context-Aware Fixes: The AI understands the application's architecture and suggests fixes that fit the codebase style
- Explanation and Education: Each suggested fix includes explanation of the vulnerability and why the fix works
- Pull Request Ready: Generated fixes can be directly committed or reviewed as pull requests
GitHub Copilot Coding Agent
- Extended Problem-Solving: The agent can coordinate multi-file changes needed for complex fixes
- Testing Integration: The agent can suggest and run tests to verify fixes don't break functionality
- Best Practice Recommendations: Agent suggests not just fixes, but security best practices for similar code patterns
- Learning Opportunity: Developers see patterns and solutions that improve their security knowledge
Human-in-the-Loop Workflow
AI-suggested fixes go through a quality gate:
- AI Suggestion: Copilot generates fix options
- Developer Review: Developer evaluates and potentially refines the suggestion
- Testing: Automated tests validate the fix doesn't break functionality
- Security Validation: Security team optionally reviews critical fixes
- Deployment: Fix is merged and deployed with confidence
Real-World Scenario: A developer receives a GitHub issue about a SQL injection vulnerability in a database query. Rather than manually researching secure query patterns, Copilot Autofix immediately suggests using parameterized queries with the specific syntax for their database. The agent also identifies three other similar vulnerable patterns in the codebase and suggests fixes for those as well. The developer reviews the suggestions, runs tests to validate they work, and the entire fix set is deployed within 30 minutes rather than the day or more it would have taken for manual remediation.
Implementation Architecture
How the Integration Works
The native integration creates a secure, real-time data flow:
GitHub Repository
↓ (Code scanning results)
GitHub Advanced Security
↓ (Vulnerability data)
Integration Bridge
↓ (Runtime context correlation)
Microsoft Defender for Cloud
↓ (Threat intelligence)
Microsoft Sentinel (optional)
↓ (SIEM integration)
Security Operations CenterData Flow
- GitHub Advanced Security scans code and identifies potential vulnerabilities
- Defender for Cloud monitors runtime behavior and identifies actual threats
- Integration Layer correlates code vulnerabilities with runtime context
- Risk Scoring Engine prioritizes issues based on exploitability and threat level
- Notification System alerts developers and security teams with useful information
Security Considerations
The integration maintains security through:
- Encrypted Communication: All data in transit is encrypted
- Identity-Based Access: Integration respects GitHub and Azure RBAC
- Audit Logging: All correlation and alerting activity is logged for compliance
- Data Residency: Data remains in customer-designated regions
- No Code Exposure: Runtime analysis doesn't require storing application code in Defender
The Unified Security Portal: One Dashboard, Complete Visibility
Microsoft is consolidating its security offerings into the unified Microsoft Defender security portal, bringing together threat detection, investigation, and posture management across all your environments. Defender for Cloud is now available in preview in this unified experience, which means your GitHub organizations can be monitored right alongside your cloud infrastructure.
What You Get in the Unified Portal
In the unified security portal, you now see:
Cloud Security Operations
| Feature | Description |
|---|---|
| Cloud Overview Dashboard | Centralized view of your cloud security posture, highlighting top improvements and security trends |
| Cloud Asset Inventory | Complete inventory of all your cloud and code assets across Azure, AWS, GCP—plus GitHub repositories |
| Incidents and Alerts | Unified incident management across cloud, endpoint, identity, and now code-level threats |
| Advanced Hunting | Correlate security data across all your environments to identify sophisticated attack patterns |
Posture Management Unified Experience
| Feature | Description |
|---|---|
| Cloud Secure Score | Risk-based scoring that actually reflects your exploitable exposure, not just theoretical vulnerability counts |
| Recommendations | Prioritized remediation guidance integrated with Microsoft Security Exposure Management |
| Attack Paths | Visual representation of how attackers could move through your infrastructure, highlighting the path of least resistance |
| Cloud Vulnerabilities | Vulnerability data correlated with runtime context—so you see what's actually exploitable |
Configuration & Control
| Feature | Description |
|---|---|
| Cloud Scopes & RBAC | Organize Azure subscriptions, AWS accounts, GCP projects, and now GitHub organizations into logical business units with granular access control |
| Response Actions | Automated response capabilities that can trigger across cloud, endpoint, and now code-level detections |
The Transition: Azure Portal to Unified Portal
Microsoft is in a transition period—and that's important to understand:
Where you are now (Preview Phase):
- GitHub organizations are added and initially configured in Azure portal (traditional Defender for Cloud)
- You can view all security data—code scanning, runtime threats, posture—in the unified security portal
- This gives you the best of both: configuration power in Azure, operational insights in the unified portal
Where this is headed:
- Eventually, you'll be able to configure everything directly in security.microsoft.com
- GitHub organization management will move from Azure portal to unified portal
- All remediation, escalation, and response workflows will be available in one place
- Microsoft is committed to feature parity—if it works in Azure portal today, it'll work in the unified portal tomorrow
- Initial setup still happens in Azure portal
- Daily operations shift to security.microsoft.com
- Configuration management will gradually move to the unified portal over the coming months
- Your learning investment is protected—concepts learned in Azure portal directly transfer to unified portal as features migrate
- GitHub Advanced Security enabled (it's included with GitHub Enterprise or you can enable it on public repositories)
- GitHub Actions enabled so automation can run
- Either a GitHub organization admin or someone with the appropriate permissions to create the integration
- An Azure subscription with workloads that Defender for Cloud should monitor
- Defender for Cloud enabled (you probably already have this, but confirm)
- Appropriate permissions to create the connection (typically Identity Governance Administrator or Security Administrator)
- Basic network connectivity between GitHub and Azure (this happens over standard internet, no special networking required)
- A GitHub Personal Access Token or GitHub App for secure authentication
- Enable scanning on new repositories from day one
- Use branch protection rules to catch issues before merge
- Require security reviews for high-risk changes
- Provide security training focused on common vulnerabilities
- Use AI suggestions as teaching opportunities
- Share lessons learned from security incidents
- Automatic scanning on every commit
- Automated remediation suggestions through Copilot
- Automated testing to validate fixes
- Keep security discussions in development tools (GitHub)
- Document security decisions and rationale
- Make security a part of code review culture
- Track mean time to remediation (MTTR) for vulnerabilities
- Monitor false positive rates and adjust rules accordingly
- Regularly review security metrics and trends
- Automatic scanning on every commit
- Automated remediation suggestions through Copilot
- Automated testing to validate fixes
- Keep security discussions in development tools (GitHub)
- Document security decisions and rationale
- Make security a part of code review culture
- Track mean time to remediation (MTTR) for vulnerabilities
- Monitor false positive rates and adjust rules accordingly
- Regularly review security metrics and trends
- Fewer late-stage security findings means fewer rework cycles
- Automated remediation reduces manual security review burden
- Clear prioritization means less time wasted on non-critical issues
- Code-level findings are validated against runtime behavior
- Only actually exploitable issues are prioritized
- Historical data improves ML model accuracy over time
- Creating complete audit trail from vulnerability discovery to remediation
- Enabling policy enforcement at the code level
- Providing evidence of security monitoring and remediation
- Supporting regulatory requirements for secure development practices
- On-premises applications can be monitored by Defender for Cloud via Arc
- GitHub repositories can contain code for any platform or technology
- The correlation works regardless of where code runs or how it's deployed
- GitHub Advanced Security catches code issues at commit time
- Copilot Autofix suggests remediation automatically
- Developers merge with confidence knowing issues are addressed
- Defender for Cloud provides runtime validation
- Result: No reduction in velocity, improved security posture
- Automated code scanning ensures compliance violations are caught early
- Runtime context from Defender shows which vulnerabilities actually pose risk
- Clear audit trail of all security decisions supports compliance audits
- AI-suggested fixes accelerate remediation without compromising quality
- Result: Compliance requirements met with less manual effort
- Centralized visibility in Defender for Cloud across all repositories
- Automated alerts when vulnerable dependencies are introduced
- Coordinated remediation across dependent systems
- Supplier security posture visible in Defender dashboards
- Result: Supply chain risk significantly reduced
- Vulnerabilities get fixed before they become production incidents
- Your development teams stop thinking of security as an obstruction and start seeing it as enablement
- Your security team reduces alert fatigue from thousands of false positives and focuses on what actually matters
- Your organization builds applications that are fundamentally more secure—not because of compliance requirements, but because security is woven into the development process
- Microsoft Ignite 2025 Book of News: The official announcement and context
- Defender for Cloud in Defender Portal: How to access Defender for Cloud in security.microsoft.com
- Azure Portal vs Defender Portal Comparison: Feature parity tracking as it evolves
- Defender for Cloud Documentation: Complete reference guide
- GitHub Advanced Security Documentation: Everything you need to enable and configure GitHub's security features
- DevSecOps Best Practices: Learn the mindset and practices behind this integration
Feature Parity: The Direction of Travel
Here's the key thing to understand: Microsoft is moving aggressively toward feature parity. Some capabilities exist only in Azure portal today (like custom recommendations and governance workflows), but that's temporary. The unified portal is the future.
As you implement this integration, understand that:
This transition isn't about abandoning Azure portal; it's about giving you options and gradually consolidating everything into one professional security operations center.
Feature Comparison: Azure Portal vs. Unified Portal
Here's a snapshot of where things stand today. Note that this comparison evolves—capabilities marked as "Azure portal only" are often coming to the unified portal soon:
| Capability | Azure Portal | Unified Portal |
|---|---|---|
| Security Recommendations | ✅ Yes | ✅ Yes (Integrated into Exposure Management) |
| Asset Inventory | ✅ Yes | ✅ Yes |
| Secure Score | ✅ Yes | ✅ Yes (New risk-based scoring) |
| Attack Path Analysis | ✅ Yes | ✅ Yes (Integrated into Exposure Management) |
| Cloud Vulnerabilities | ✅ Yes | ✅ Yes |
| Incident & Alerts | ✅ Yes | ✅ Yes |
| Advanced Hunting | ✅ Yes | ✅ Yes |
| Data Visualization with Workbooks | ✅ Yes | ⏳ Coming |
| Data Exporting | ✅ Yes | ⏳ Coming |
| Workflow Automation | ✅ Yes | ⏳ Coming |
| Quick Fixes & Remediation | ✅ Yes | ⏳ Coming |
| Risk Hunting with Explorer | ✅ Yes | ⏳ Coming |
| ServiceNow Integration | ✅ Yes | ⏳ Coming |
| Governance & Scale | ✅ Yes | ⏳ Coming |
| Cloud Scopes & RBAC | ✅ Yes | ✅ Yes |
| Agentless VM Scanning | ✅ Yes | ✅ Yes |
| Container Code-to-Cloud Mapping | ✅ Yes | ✅ Yes |
| IaC Code-to-Cloud Mapping | ✅ Yes | ✅ Yes |
| Data Security Posture Management | ✅ Yes | ✅ Yes |
| API Security Posture | ✅ Yes | ✅ Yes |
Getting Started: Making the Connection
Ready to connect your GitHub organizations to Defender for Cloud? Here's what you need in place. Don't worry—none of this is particularly complex.
What You'll Need
On the GitHub side:
On the Azure side:
For the connection itself:
Getting the Connection Working
Step 1: Make GitHub Ready
You'll want code scanning turned on first. Jump into your GitHub repository settings and enable Advanced Security features—specifically code scanning, secret scanning, and dependency scanning. This starts the intelligence gathering.
Step 2: Wire It Into Defender
Head to Defender for Cloud (in Azure portal), find Environment Settings, and look for GitHub Connectors. Create a new connection and authenticate with GitHub. This is where the two platforms start talking.
Step 3: Decide What Matters
Configure which code scanning results should bubble up as priority in Defender. You don't need every finding with the same urgency—customize the prioritization so what reaches your security team is actually important.
Step 4: Enable Your Developers
Set up GitHub Actions to run automated remediation suggestions. Enable Copilot Autofix if you're using GitHub Copilot. Configure branch protection so risky code doesn't merge without security review. This turns security from a gate into part of the workflow.
Step 5: Keep Your Eyes Open
Monitor how well this is working. Look at your mean time to remediation (MTTR). Adjust rules if you're seeing noise. Update policies as your organization and threat environment evolve.
That's it. Nothing revolutionary, just sensible security automation.
Best Practices for DevSecOps
1. Integrate Early, Fail Fast
2. Enable Developers
3. Automate Everything Possible
4. Maintain Context
5. Measure and Improve
4. Maintain Context
5. Measure and Improve
Addressing Common Concerns
"Will this slow down development?"
No, quite the opposite. By catching issues early and providing automated fixes, the integration actually accelerates development:"What about false positives?"
GitHub Advanced Security and Defender for Cloud both use runtime context and machine learning to minimize false positives. When correlated together, false positive rates decrease further because:"How does this affect compliance?"
The integration improves compliance posture by:"What about legacy applications or on-premises workloads?"
The integration works across hybrid environments:Real-World Implementation Scenarios
Scenario 1: SaaS Company with Rapid Release Cycle
Challenge: Releases happen multiple times per week, and security concerns slow down development Solution:Scenario 2: Financial Services Organization
Challenge: Strict compliance requirements and extensive security review processes Solution:Scenario 3: Enterprise with Complex Supply Chain
Challenge: Multiple teams, multiple vendors, complex dependencies Solution:What You Can Actually Do with Defender for Cloud (Complete Feature Set)
If you're wondering whether Defender for Cloud is mature enough for your organization, here's the complete feature set available to you right now:
Cloud Security Operations
| Feature | What It Does |
|---|---|
| Cloud Overview Dashboard | Your security control center showing key metrics, top improvement actions, and trend analysis across your entire cloud footprint |
| Cloud Asset Inventory | Complete visibility into every asset across Azure, AWS, GCP, and GitHub—organized by workload, criticality, and coverage level |
Posture Management
| Feature | What It Does |
|---|---|
| Cloud Secure Score | Risk-based scoring that weighs exploitability and threat level, not just vulnerability counts |
| Recommendations | Prioritized, practical security improvements with guidance and (in many cases) one-click remediation |
| Attack Paths | Visual representation of how an attacker could traverse your infrastructure—showing your most dangerous exposure |
| Cloud Vulnerabilities | Unified view of all vulnerabilities with context about actual exploitability in your environment |
Threat Detection & Response
| Feature | What It Does |
|---|---|
| Incidents and Alerts | Correlated security events that tell a story of what's happening across your infrastructure |
| Response Actions | Automated playbooks and manual actions to contain and remediate threats in real-time |
| Advanced Hunting | Query-based investigation to hunt for sophisticated threats and validate incident response |
Configuration & Control
| Feature | What It Does |
|---|---|
| Cloud Scopes & RBAC | Organize resources by business unit with granular role-based access control—so people see only what they need |
This complete feature set is available both in Azure portal and gradually rolling into security.microsoft.com.
Where This Actually Takes You
Let's be direct: this integration represents a fundamental shift in how application security works. You're not just getting two tools talking to each other; you're getting a complete security framework that understands your applications from the moment code is committed through every moment it runs in production.
The practical reality:
This is DevSecOps that actually works, powered by cloud-native architecture and AI-assisted remediation. It's not a theoretical best practice; it's what modern application security looks like in 2025.
The unified portal in security.microsoft.com is the control center. Start in Azure portal for configuration. Build your implementation. Then watch as Microsoft rapidly brings parity features to the unified experience. This is where your organization's security operations is headed—one integrated dashboard, complete visibility, and the ability to see threats from code to runtime.
Resources & Next Steps
Want to dive deeper? Here are the resources to get you started:
Ready to bring your development and security teams together? Start with the GitHub integration in Defender for Cloud. Connect your first repository. See how code-scanning findings correlate with runtime threats. Experience the difference that unified visibility actually makes.
Your future security operations are waiting—starting with a single integration, expanding to complete visibility, ending with code and runtime threats handled together instead of in silos.
