Microsoft Sovereignty 2026: Deployment & Operations Reality — Part 10
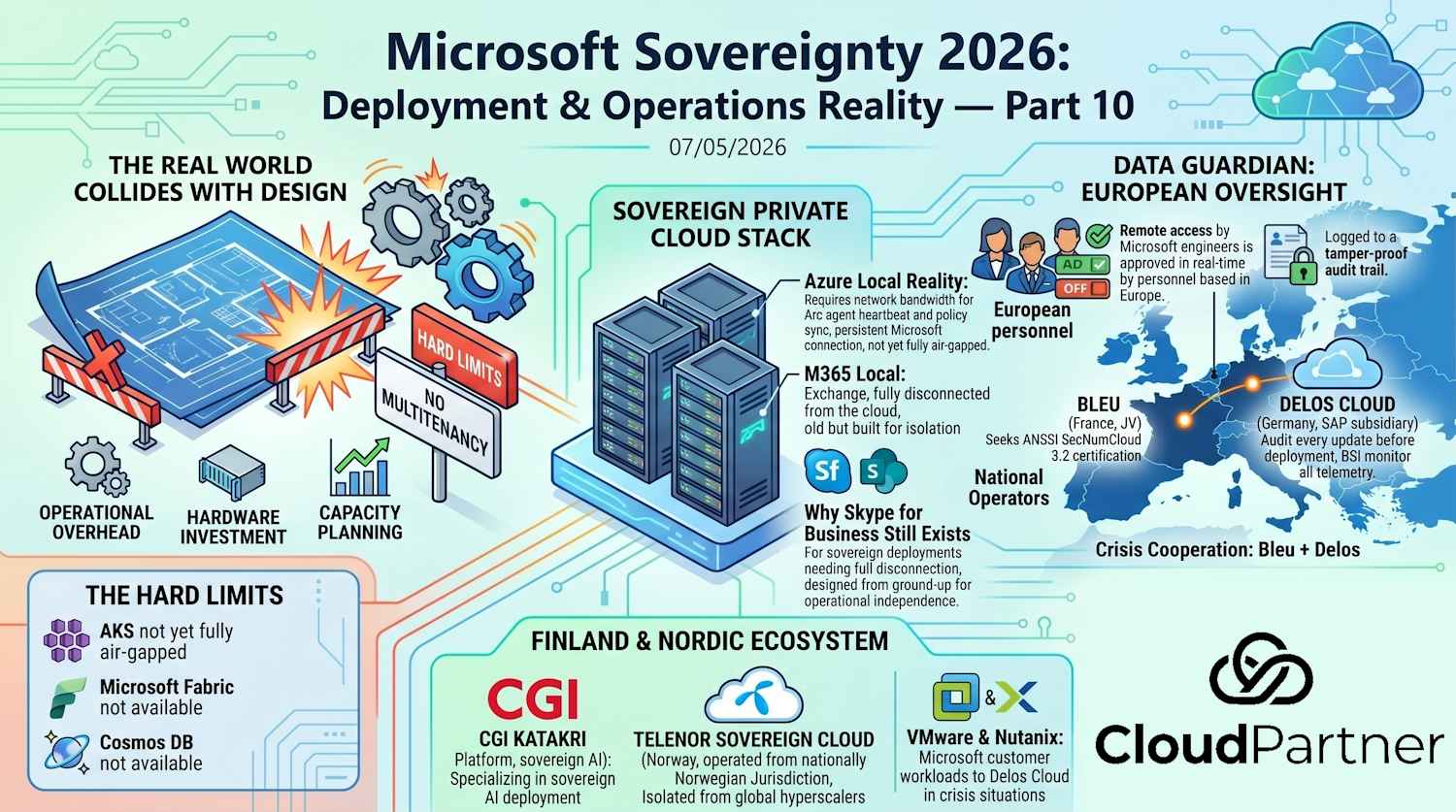
If Part 9 covered the encryption architecture and control plane theory, Part 10 is where the real world collides with the design. This is what actually gets deployed, where you hit hard limits, and how national operators fit into Microsoft's sovereignty stack.
Sovereign Private Cloud Stack
In February 2026, Microsoft announced a complete stack that's supposed to make organizations independent from cloud infrastructure entirely. Here's what's in it and what actually works.
Azure Local Reality
Azure Local runs Azure infrastructure on your premises with Microsoft governance and policies. It scales now to thousands of servers (April 2026 update: disaggregated architecture with SAN storage support).
This is genuinely capable. But it requires:
- Thousands of euros in hardware investment (Azure Stack HCI certified servers, NVIDIA GPUs if you want acceleration)
- Network bandwidth for Arc agent heartbeat and policy sync
- Your own operations team — Azure Local doesn't run itself
- Capacity planning and scaling — you can't just "add more cloud"
The appeal: you run Azure on your infrastructure, subject to your physical security, your policies, your compliance regime.
M365 Local: Skype for Business, Really
Microsoft 365 Local means Exchange Server, SharePoint Server, and — this is where it gets interesting — Skype for Business Server running on customer premises, fully disconnected from the cloud.
Yes, Skype for Business. Not Teams.
Why Skype for Business Still Exists
To understand why Microsoft keeps SfB around for sovereign deployments, you need to understand enterprise voice infrastructure. Big enterprise voice deployments with high-availability are genuinely complex — we're talking multiple geographic regions, failover clustering, media gateway redundancy, carrier trunking integration, E911 routing policies, and compliance requirements that vary by jurisdiction.
Skype for Business Server was built from the ground up for that complexity. It's designed to sit on premises, manage media streams locally, integrate with existing PBX infrastructure and carrier connections, and operate fully independently if the cloud connection drops. High-availability SfB deployments involve active-active clusters, database replication, DNS load balancing, and careful orchestration of every component.
Microsoft essentially took that entire architecture, all the enterprise voice complexity, all the on-premises operational knowledge, and ported it to the cloud. They added modern clients, better presence detection, Skype meeting integration, federation — but at its heart, Teams is still built on the same foundational concepts that made SfB enterprise-grade. Yes, Teams does a lot more: instant messaging, file sharing, persistent chat, extensibility. But the core infrastructure problem Teams solves is the same problem SfB solved — reliable, compliant voice and video communications at enterprise scale.
The difference: Teams assumes cloud connectivity. SfB doesn't. For sovereign deployments that genuinely need full disconnection, you need the version that was architected for on-premises isolation and operational independence.
And honestly, it makes sense. Teams is cloud-native. It doesn't work without the cloud. If you need a fully disconnected communication system, you need something designed for that. Skype for Business is old, but it's built for on-premises operation.
If your organization genuinely can't have any cloud connectivity for messaging and collaboration, you're also not running modern authentication, modern compliance, or modern anything else. Full disconnection has serious trade-offs — understand them before committing.
Foundry Local is the AI piece — large models on your NVIDIA hardware within strict sovereignty boundaries. It's available to select customers only, and we don't have broad pricing or SLAs yet.
The Hard Limits
Here's where marketing meets reality:
| Component | Status | Reality |
|---|---|---|
| AKS (fully air-gapped) | Not yet | AKS still needs Azure Arc connectivity for management |
| Large-scale disconnect | Partial | Single-rack disconnected mode exists but is too small for real workloads. Multi-rack requires persistent Microsoft connection. |
| Microsoft Fabric | Not available | No sovereign version. Data analytics stays in cloud-dependent territory. |
| Cosmos DB | Not available | No sovereign version for now. |
| Azure OpenAI | Not available | AI inference is Foundry Local only, select customers. |
| Multitenancy | Missing | Every customer needs their own cluster. Microsoft says multitenancy is coming, but scope unclear. |
The fundamental tension: the small, truly disconnected version doesn't scale to serious production. The large, scalable version still needs a persistent connection to Microsoft. The disconnected version is theater unless you're running a very small workload.
Important: Multitenancy is missing. Today, every customer needs their own dedicated cluster. VMware and Nutanix already offer this. Microsoft has confirmed multitenancy is coming, but it's unclear whether that's for connected mode, disconnected mode, or both.
Data Guardian: European Oversight
In June 2025, Microsoft announced Data Guardian: all remote access by Microsoft engineers to European customer data is approved in real time by personnel based in Europe and logged to a tamper-proof audit trail.
If a support engineer in the US or India needs to access your European data, a European operator must approve it in real time. It gets logged. It's verifiable.
This is a concrete technical layer on top of the contractual Data Processing Agreement (DPA) commitments.
Skeptical Note: Some analysts call this "sovereignty-washing." A European operator can block routine access — true. But if the US government issues a CLOUD Act-based legal order to Microsoft at the corporate level, that's not solved by a technical layer. A European gatekeeper doesn't change the legal reality. Be realistic about what this solves.
Data Guardian is useful for audit trails and routine access control. It doesn't change fundamental jurisdiction questions.
DPA Appendix D: Contractual Protection and Its Limits
Microsoft's Data Protection Addendum (DPA) includes a special clause for EU public sector customers called Appendix D. Here's what it actually promises — and what it doesn't.
Get the DPA: You can download the full Microsoft Data Processing Agreement and Appendix D documentation to review the exact contractual commitments.
If any government — including the US — orders Microsoft to suspend cloud services, Microsoft commits to:
- Using available means to seek voluntary withdrawal or rescission of such an order
- Challenging the order in the courts of the country that issued it
- Seeking interim injunctive relief to ensure service continuity during legal proceedings
This applies to national, federal, and regional government customers of EU member states — not the private sector.
Honest Assessment: Strong contractual language on paper. But here's the reality: a CLOUD Act-based legal process takes time. Services could be suspended before a final ruling. Data Guardian, EKM, and Appendix D form layers of protection — but a corporate-level legal order bypasses all of them contractually.
The CLOUD Act Context: The US CLOUD Act gives US law enforcement and intelligence agencies the power to compel US companies (including Microsoft) to disclose customer data stored anywhere in the world — including Europe. This applies regardless of where the data physically resides. No national borders, no local data residency rules protect you from a CLOUD Act order at the corporate level.
Appendix D doesn't change that legal reality. What it does is add contractual commitments from Microsoft to fight the order — which is real value, but it's not a technical solution.
National Operators: Europe's Alternative Approach
While Microsoft builds sovereign solutions, France and Germany took a different approach: they built national operators that own the infrastructure entirely. This is the real alternative to Microsoft sovereignty.
Bleu — France
Bleu is a 50/50 joint venture between Capgemini and Orange. It offers Microsoft Azure and M365 services — but the data centers are physically separate from Microsoft and French-owned. The goal is ANSSI SecNumCloud 3.2 certification, a legal requirement under France's "cloud au centre" doctrine for trusted cloud services in the public sector.
Customers include EDF, Dassault Aviation, and Crédit Mutuel. Bleu is also part of the Gaia-X ecosystem. The model: Microsoft supplies the technology, but Capgemini and Orange own the operation and infrastructure.
Delos Cloud — Germany
Delos Cloud is a subsidiary of SAP. It offers Azure and Office 365 services — but Microsoft only supplies the software. Delos owns the service, Arvato Systems operates the data centers. Germany's BSI (Bundesamt für Sicherheit in der Informationstechnik) monitors all telemetry and audits every update before deployment. Microsoft cannot see data in the Delos Cloud. Infrastructure is physically separate from Microsoft.
The model is built around BSI's requirements for public sector cloud services — rigorous, audited, and German-controlled.
Crisis Cooperation: Bleu + Delos
Here's where it gets interesting. Bleu and Delos have signed the Franco-German Mutual Assistance Commitment: cooperation on cybersecurity threat detection, coordinated defense, and joint response in crisis scenarios. Delos has also signed an MoU giving it the authority to migrate Microsoft customer workloads to the Delos Cloud in crisis situations — should Microsoft's services become restricted in Europe.
This is concrete geopolitical infrastructure planning, not theater. If a CLOUD Act scenario forces Microsoft to restrict European operations, German and French infrastructure exists as an actual fallback. Customer workloads can physically move to infrastructure that's not subject to US legal authority — Delos handles the mechanics.
Finland & the Nordic Sovereign Ecosystem
Finland doesn't yet have a national Microsoft partner model equivalent to Bleu or Delos. But the ecosystem is developing, and it's worth watching.
CGI launched a KATAKRI-certified sovereign AI platform in Finland in April 2026, targeting enterprises and the public sector. KATAKRI is Finland's information security certification program for critical infrastructure. The platform operates from CGI's Finnish KATAKRI-certified data center and supports deployment of multiple large language models (LLMs) via an OpenAI-compatible API, within the customer's sovereign data boundary.
Telenor Sovereign Cloud — Norway
On the same day as Microsoft Digital Sovereignty Day Finland (May 5, 2026), Telenor announced Telenor Sovereign Cloud — a new Norwegian sovereign cloud company built from the ground up for organizations with stringent requirements for security, resilience, and regulatory compliance.
Key points:
- National Control: Operated from nationally controlled data centers in Norway, completely isolated from global hyperscalers
- Norwegian Jurisdiction: All data stored, processed, and managed under Norwegian law
- Initial Targets: Public sector and large enterprises in energy and healthcare sectors
- Pilot Phase: Telenor working with selected customers to test the platform before broader commercial launch
- Commercial Launch: Planned for H1 2027 (first half of 2027)
- Team & Capability: Telenor recruiting ~50 specialist staff in security, cloud, and infrastructure
- Model: Standalone company under Telenor Infrastructure, built with selected technology partners but retaining full control of architecture, operations, and security
Telenor Sovereign Cloud is basically Norway's answer to Bleu and Delos — a Nordic telecom operator building infrastructure that stays under Nordic control. Geopolitical uncertainty and hyperscaler dependency are driving this. It's the Scandinavian version of what Germany and France already did.
Nordic Sovereign Strategy: Telenor Sovereign Cloud starts in Norway with full Norwegian control and jurisdiction, with potential expansion to other Nordic countries. It's a full-stack sovereign alternative to hyperscaler infrastructure — not just a companion service. CGI's KATAKRI platform (Finnish, April 2026) takes a different approach: specializing in sovereign AI deployment that can sit alongside Microsoft services. Organizations may mix both approaches: Azure Local for core compute, Telenor for Nordic-jurisdiction workloads, KATAKRI for regulated AI workloads in Finland.
The Nordic ecosystem is building. Not with the centralized national operator model like Bleu or Delos, but with distributed sovereign capabilities — each country developing its own answer to the control and jurisdiction questions. Expect this to expand as other Nordic operators (Sweden, Denmark) follow.
Foundry Local: Sovereign AI Model Deployment
Buried in the sovereignty announcements is Foundry Local — Microsoft's sovereign AI infrastructure for large language models. This is fundamentally different from Azure OpenAI.
What Foundry Local Is
Foundry Local runs large AI models (LLMs, multimodal models, or custom fine-tuned models) on your own NVIDIA hardware infrastructure, within strict sovereignty boundaries. Your data never leaves your environment. Your models never touch Microsoft's cloud training pipelines.
How It Differs from Azure OpenAI
| Aspect | Azure OpenAI | Foundry Local |
|---|---|---|
| Data Residency | Azure region (still cloud-hosted) | Customer premises only |
| Model Location | Microsoft-managed infrastructure | Your NVIDIA hardware |
| Training Data | Sent to Microsoft infrastructure | Stays local, never sent to Microsoft |
| Control | Microsoft manages everything | You manage hardware & deployment |
| Pricing | Pay-per-token model | TBD - likely fixed hardware costs |
| Availability | General availability | Select customers, limited preview |
Availability & Access
Foundry Local is restricted to select customers only — likely large enterprises with significant AI workloads and the infrastructure to support it. If you need sovereign AI and can justify the cost, Foundry Local is available today. If you're waiting for public launch, expect at least 18-24 months.
Important Caveat: Foundry Local pricing and SLAs are not yet public. Microsoft hasn't disclosed whether this is a subscription, a per-deployment fee, or hybrid pricing. Factor this into your planning.
VMware & Nutanix: Why They Matter for Comparison
The Hard Limits table mentions that VMware and Nutanix already offer multitenancy — something Microsoft doesn't yet support in Azure Local. Here's why that comparison matters.
VMware Sovereign Cloud
VMware offers a sovereign cloud solution where customers deploy vCloud on their premises. It supports multitenancy natively, meaning multiple customers can share infrastructure with complete isolation. VMware handles infrastructure abstraction; you don't need deep Kubernetes or Azure knowledge. The downside: you're building a proprietary cloud, not standard Microsoft or Azure.
Nutanix Sovereign
Nutanix offers hyper-converged infrastructure with multitenancy baked in. Organizations deploy Nutanix clusters on-premises and manage workloads with complete tenant isolation. It's vendor-neutral (supports Kubernetes, traditional VMs, databases) and handles the multi-customer complexity that Azure Local currently doesn't.
Why This Matters
If you're a service provider or hosting company wanting to offer sovereign infrastructure to multiple customers (subsidiaries, business units, external clients), VMware and Nutanix are production-ready today. Azure Local requires every customer to have their own dedicated cluster — which is expensive at scale. This is Microsoft's biggest gap in the sovereign infrastructure story.
If multitenancy matters to your business (multiple customers on shared infrastructure), Azure Local isn't ready yet. VMware and Nutanix have this working today. If that's your requirement, they're the safe choice right now.
Gaia-X Ecosystem: Europe's Cloud Infrastructure Initiative
You'll see Gaia-X mentioned in sovereign cloud discussions. What is it and why does it matter?
Gaia-X is a European initiative to create a federated cloud infrastructure ecosystem that keeps data and services within Europe. It's not a single cloud provider — it's a framework and set of standards that multiple providers can join.
Who's in Gaia-X
- Bleu (Capgemini + Orange) — Microsoft partner in France
- Delos Cloud (SAP) — not formally Gaia-X but aligned
- OVHcloud, Deutsche Telekom, Vodafone, and others
Essentially, Gaia-X is the European counter-narrative to "everything goes to AWS/Azure/Google" cloud. It's a commitment to keeping infrastructure federated and European-controlled.
Why Bleu Is Gaia-X Important
Bleu being part of Gaia-X means it's not just Capgemini's private solution — it's part of a larger European ecosystem. If you implement Bleu, you're stepping into infrastructure that's designed to interoperate with other Gaia-X providers. This theoretically gives you exit options and vendor flexibility.
Practical Take: Gaia-X is politically important and architecturally sound, but it's still building. Don't assume seamless interoperability yet. Think of it as "the intention is there" rather than "it's fully standardized."
Operational Reality: What It Takes to Run Azure Local
Azure Local isn't like managing cloud resources through the portal. You need actual infrastructure operations expertise.
Required Staffing
- 1-2 Infrastructure Engineers: Day-to-day cluster operations, hardware management, patching, firmware updates
- 1 Security Officer: Network isolation, access control, compliance audit logging
- Optional Network Engineer: If you're running hybrid with cloud connectivity (which you probably are)
- Optional Kubernetes Specialist: Depends on workload complexity; some teams use Azure Arc for management assistance
Skill Requirements
- Deep understanding of hyperconverged infrastructure (HCI)
- Storage management (SAN/NAS integration)
- Network isolation and security
- Azure management (even though it's on-prem, Azure tooling is used for updates and diagnostics)
- Physical infrastructure (power, cooling, security)
This isn't a "buy it and forget it" solution. If you're serious about Azure Local, you're running a data center operation.
Design & Planning Tooling: Azure Odin
If you're building the operational team described above, your Infrastructure Engineers will spend weeks designing the deployment: hardware sizing, network topology, storage configuration, IP planning, and security settings. This is where Azure Odin becomes invaluable.
Azure Odin is Microsoft's web-based wizard for designing Azure Local architectures. It's not a deployment tool — it's a planning and design assistant that removes guesswork from decisions you'll make dozens of times:
- Hardware Sizer: Input your workloads (VMs, AKS Arc, AVD, Foundry Local) and Odin calculates CPU, memory, disk, GPU, power, and rack-space requirements with real OEM hardware models
- Deployment Scenarios: Choose Hyperconverged, Disaggregated (external SAN), Multi-Rack, Disconnected, or Microsoft 365 Local — each with guided configuration steps
- Network Design: Network intent mapping, storage VLAN configuration, CIDR calculator, and switchless vs. switched topology options
- Switch Configuration Generator: Auto-generate Top of Rack (ToR) switch configurations for Cisco NX-OS and Dell OS10, complete with QoS validation against Azure Local requirements
- Export Formats: Generate ARM parameters JSON for automated deployment, Markdown/Word/PowerPoint configuration reports, or import existing ARM templates to iterate
- 3D Rack Visualization: See your hardware layout before you buy — interactive 3D rack diagrams with node positioning, cable routing, and power estimates
Available at https://aka.ms/ODIN (online) or run locally. It's client-side only — no data leaves your browser. Your Infrastructure Engineers can export their final configuration and hand it off to procurement and deployment teams with complete confidence in sizing and network topology.
Azure Odin doesn't replace infrastructure expertise — it amplifies it. Your team still needs to understand network requirements, workload profiles, and compliance constraints. But Odin removes the tedious math. It gives you validated hardware configurations, network diagrams, and export templates in hours instead of weeks of manual calculation.
Honest Assessment: Many organizations underestimate the operational overhead. Azure Local is cloud-like in interface but infrastructure-like in execution. Budget for expertise accordingly. Having the right design tooling (like Odin) significantly reduces deployment timelines.
Exit Strategy & Vendor Lock-In Risks
Here's a question most organizations don't ask until it's too late: what if you need to leave?
Bleu & Delos Lock-In
If you're running on Bleu or Delos Cloud, your workloads are running on their infrastructure with their tools. Exiting looks like:
- Data export: Can you get all your data out (Exchange mailboxes, SharePoint sites, Teams data)?
- Configuration export: Can you export Microsoft Entra ID, policies, and configuration?
- Workload migration: Can you migrate Kubernetes workloads or VMs to another cloud (AWS, Azure public, Azure Local)?
- Timeline: How long does this take? Weeks? Months?
Neither Bleu nor Delos have published detailed exit procedures. This is a gap. Before committing, ask explicitly: "What's the exit process if we need to migrate?"
Azure Local Lock-In
Azure Local is less of a lock-in risk (it's Microsoft technology you own), but there's still the hardware dependency. If you need to migrate off Azure Local:
- Kubernetes workloads can move to any Kubernetes cluster (AKS, EKS, GKE, on-prem)
- Windows Server and Linux VMs can move with Hyper-V export
- But you've paid for that hardware and can't easily recover that investment
Before you commit to national operators or Azure Local, ask this upfront: what's your exit plan? If Microsoft or Bleu or Delos cuts support or changes terms, can you actually leave? If the answer's no, you need to know that going in.
Support & SLAs: Cloud vs. Sovereign
Sovereign infrastructure often has different support and SLA models than standard cloud:
| Aspect | Standard Azure | Azure Local / Bleu |
|---|---|---|
| SLA | 99.9% - 99.99% depending on service | Often lower (98-99.5%) — shared infrastructure risk |
| Support Response | 15 min - 4 hours depending on severity | Depends on local support contracts; may be 1-8 hours |
| Patching | Microsoft controls and schedules | Often customer-scheduled; you decide when |
| Hardware Replacement | Microsoft's responsibility | Often customer's responsibility to manage/replace |
| Escalation Path | Microsoft support to engineering | Operator (Capgemini/Arvato/etc) → sometimes Microsoft |
The tradeoff: with sovereignty comes more control but also more operational responsibility. You're trading Microsoft SLAs for the ability to say "the data stays local."
If you need 99.99% SLAs for critical workloads, sovereign infrastructure might force you into expensive multi-site redundancy. Standard Azure already has that built-in. It's a real tradeoff — better control vs. lower guaranteed availability.
Decision Framework: Do You Actually Need This?
Not every organization needs sovereign infrastructure. Here's how to think about it:
You Probably Need Sovereignty If:
- Regulatory requirement: Your industry (financial services, critical infrastructure, defense) has explicit data residency or key control mandates
- Classified data: You handle government-classified information that cannot be in US-controlled infrastructure
- Political sensitivity: Your organization operates in geopolitically tense regions and genuinely cannot accept any US legal risk
- Physical security mandate: You're required to control the physical location of hardware processing your data
You Probably Don't If:
- Standard business data: Your data is commercial, not sensitive to jurisdiction questions
- Regulatory compliance is achievable in US clouds: GDPR, HIPAA, PCI-DSS can be met with standard Azure + proper controls
- Your real constraint is cost: If you're choosing sovereignty to "save money," you're making a mistake. Sovereignty is always more expensive.
- You want "just in case" sovereignty: If you can't articulate a specific regulatory or security requirement, you probably don't need it.
The Cost Reality:
Sovereign infrastructure costs 3-5x more than standard cloud:
- Azure Local hardware: €50,000-300,000+ depending on scale
- Staffing for on-premises operations: dedicated team
- CMK/EKM infrastructure: €300-500/month plus HSM hardware
- No shared cost benefits of massive cloud economies of scale
If budget is a constraint, sovereignty isn't the answer.
Final Take
Sovereignty solutions are real, they work, and for specific use cases they're necessary. But they're not magic. They don't eliminate jurisdictional questions — they change who owns the infrastructure. They don't provide "instant compliance" — they're one component of a compliance posture. And they cost significantly more than standard cloud.
If you have a genuine regulatory or security requirement that mandates sovereignty, the tooling is there. Deploy it correctly with proper governance. But if you're considering it for reasons of fear or "just in case," step back and honestly evaluate whether you need it.
Most organizations don't. And that's okay.
The Sovereignty Landscape in 2026
If you've made it this far through both parts of this series, here's the landscape as it actually exists right now:
The technology works. Encryption models are solid. National operators like Bleu and Delos are operational and certified. Azure Local is shipping. Foundry Local exists, even if access is restricted. The plumbing is real.
The ecosystem is still building. Gaia-X is important politically but not yet standardized. Exit procedures aren't published. VMware and Nutanix have multitenancy today; Microsoft doesn't. Finland's KATAKRI ecosystem is emerging but incomplete. This isn't a finished product — it's an architecture in motion.
Operational expectations are misaligned. Organizations expect "sovereign cloud" to work like regular cloud management — a portal, some settings, done. The reality: you're running a data center. You need infrastructure expertise, 24/7 operations capability, and deep vendor lock-in acceptance. The vendors know this. Many customers don't.
Regulatory drivers matter more than cost. If you need sovereignty because of compliance mandates (financial sector, public sector, defense), the decision is clear. If you need it because you're afraid of US government overreach or want "just in case" data sovereignty, the cost justification falls apart quickly. Be honest about why you need this.
It's not going away. Geopolitics isn't reversing. If anything, sovereignty requirements are expanding. Every region will eventually have its own trusted cloud option. This is a permanent shift in cloud architecture, not a temporary trend.
The right question isn't "should we do sovereignty?" It's "does our regulatory environment or risk posture require us to do sovereignty?" If yes, the tooling exists and you should start planning now — timelines are long, implementations are complex, and vendor lead times are substantial. If no, don't do it just because it's available. Sovereignty has a real cost.